I already host multiple services via caddy as my reverse proxy. Jellyfin, I am worried about authentication. How do you secure it?
Kinda hard because they have an ongoing bug where if you put it behind a reverse proxy with basic auth (typical easy button to secure X web software on Internet), it breaks jellyfin.
Best thing is to not. Put it on your local net and connect in with a vpn
I’m not experiencing that bug. My reverse proxy is only accessed locally at the moment though. I did have to play with headers a bit in nginx to get it working.
Basic auth. The bug is if you enable basic auth.
It is enabled, but now I’m doubting that. I’ll double check when my homelab shift is complete.
So i’ve been trying to set this up this exact thing for the past few weeks - tried all manner of different Nginx/Tailscale/VPS/Traefik/Wireguard/Authelia combos, but to no avail
I was lost in the maze
However, I realised that it was literally as simple as setting up a CloudFlare Tunnel on my particular local network I wanted exposed (in my case, the Docker network that runs the JellyFin container) and then linking that domain/ip:port within CloudFlare’s Zero Trust dashboard
Cloudflare then proxies all requests to your public domain/route to your locally hosted service, all without exposing your private IP, all without exposing any ports on your router, and everything is encrypted with HTTPS by default
And you can even set up what looks like pretty robust authentication (2FA, limited to only certain emails, etc) for your tunnel
Not sure what your use case is, but as mine is shared with only me and my partner, this worked like a charm
I’m pretty sure that using Jellyfin over Cloudflare tunnels is against their TOS, just FYI. I’m trying to figure out an alternative myself right now because of that.
I just moved from that. I now have Traefik on aVPS with a Wireguard server that my home router connects to (Immich IP forwarded in the config of WG).
Thanks for mentioning. I ended up using a Tailscale funnel and everything is running swimmingly so far.
Pay attention to your email, when cloudflare decides to warn you for this (they will, it’s very very much against TOS) they’ll send you an email, if you don’t remove the tunnel ASAP, your entire account will be terminated.
Why would Cloudflare warn me against a service they themselves offer? The email authentication is all managed by them
You’re not allowed to tunnel video traffic.
Is it just you that uses it, or do friends and family use it too?
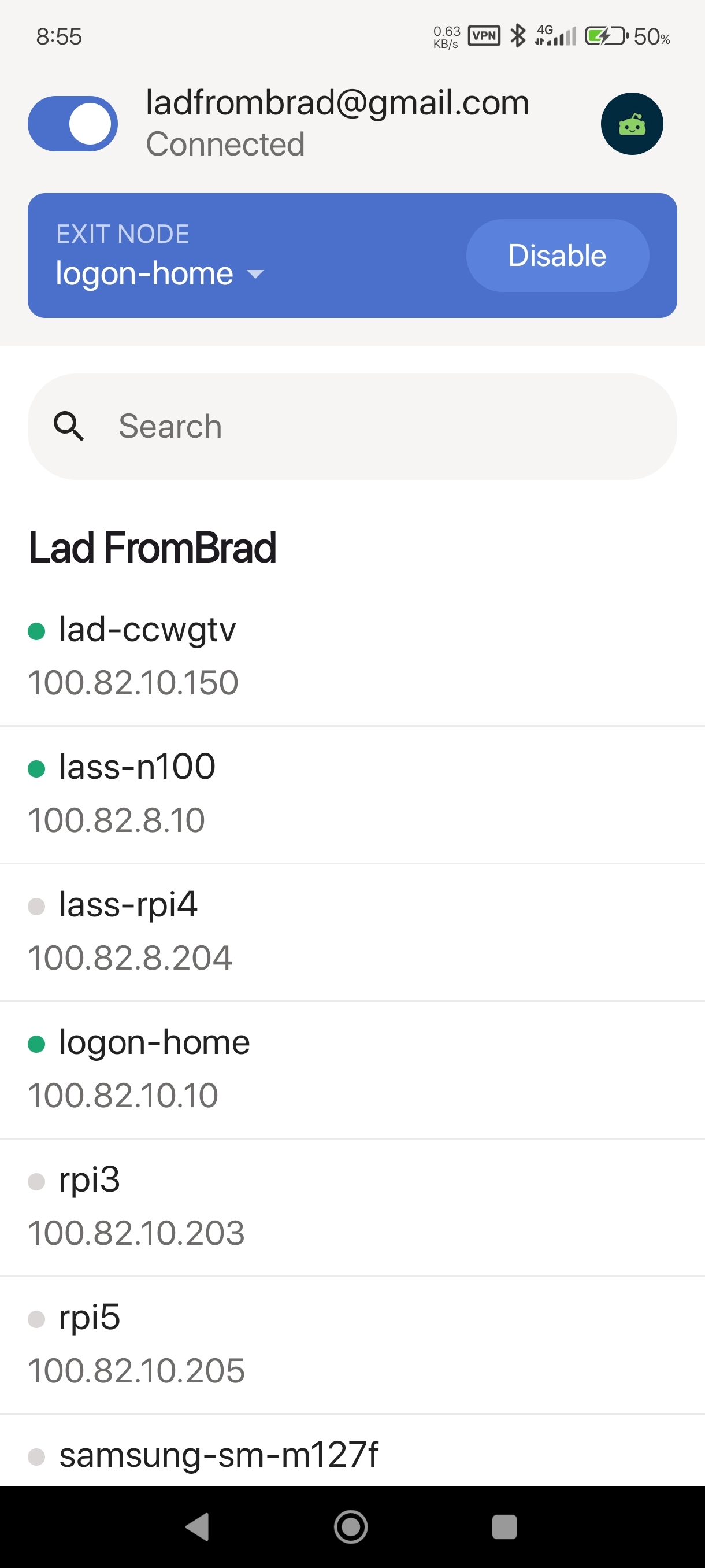
The best way to secure it is to use a VPN like Tailscale, which avoids having to expose it to the public internet.
This is what I do for our security cameras. My wife installed Tailscale on her laptop and phone, created an account, and I added her to my Tailnet. I created a home screen icon for the Blue Iris web UI on her phone and mentioned to her, “if the cameras don’t load, open Tailscale and make sure it’s connected”. Works great - she hasn’t complained about anything at all.
If you use Tailscale for everything, there’s no need to have a reverse proxy. If you use Unraid, version 7 added the ability to add individual Docker containers to the Tailnet, so each one can have a separate Tailscale IP and subdomain, and thus all of them can run on port 80.
if the cameras don’t load, open Tailscale and make sure it’s connected
I’ve been using Tailscale for a few months now and this is my only complaint. On Android and macOS, the Tailscale client gets randomly killed. So it’s an extra thing you have to manage.
It’s almost annoying enough to make me want to host my services on the actual internet… almost… but not yet.
Yeah my wife and I are both on Android, and I haven’t been able to figure out why it does that.
The Android client is open-source so maybe someone could figure it out. https://github.com/tailscale/tailscale-android
It loses its foreground notification I’ve found that kills it for me
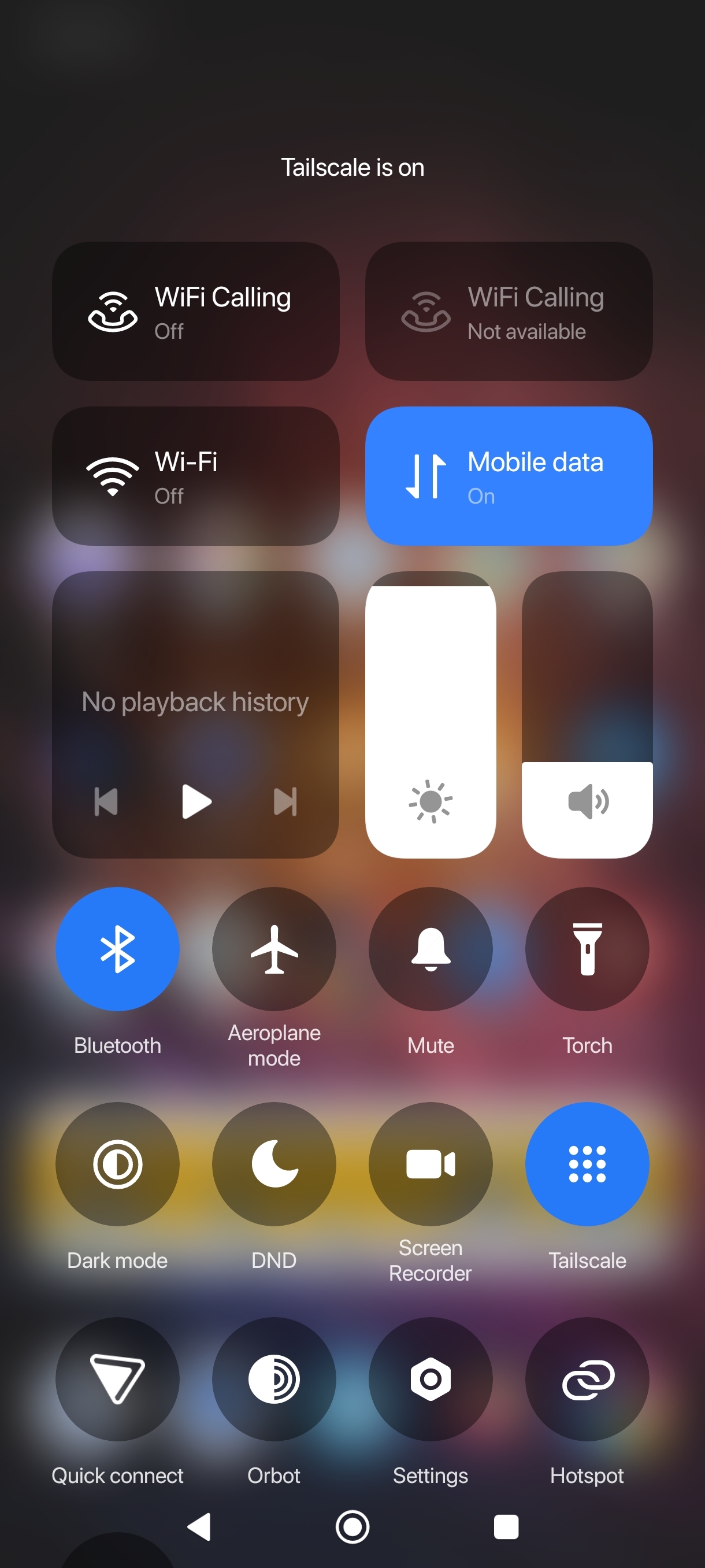
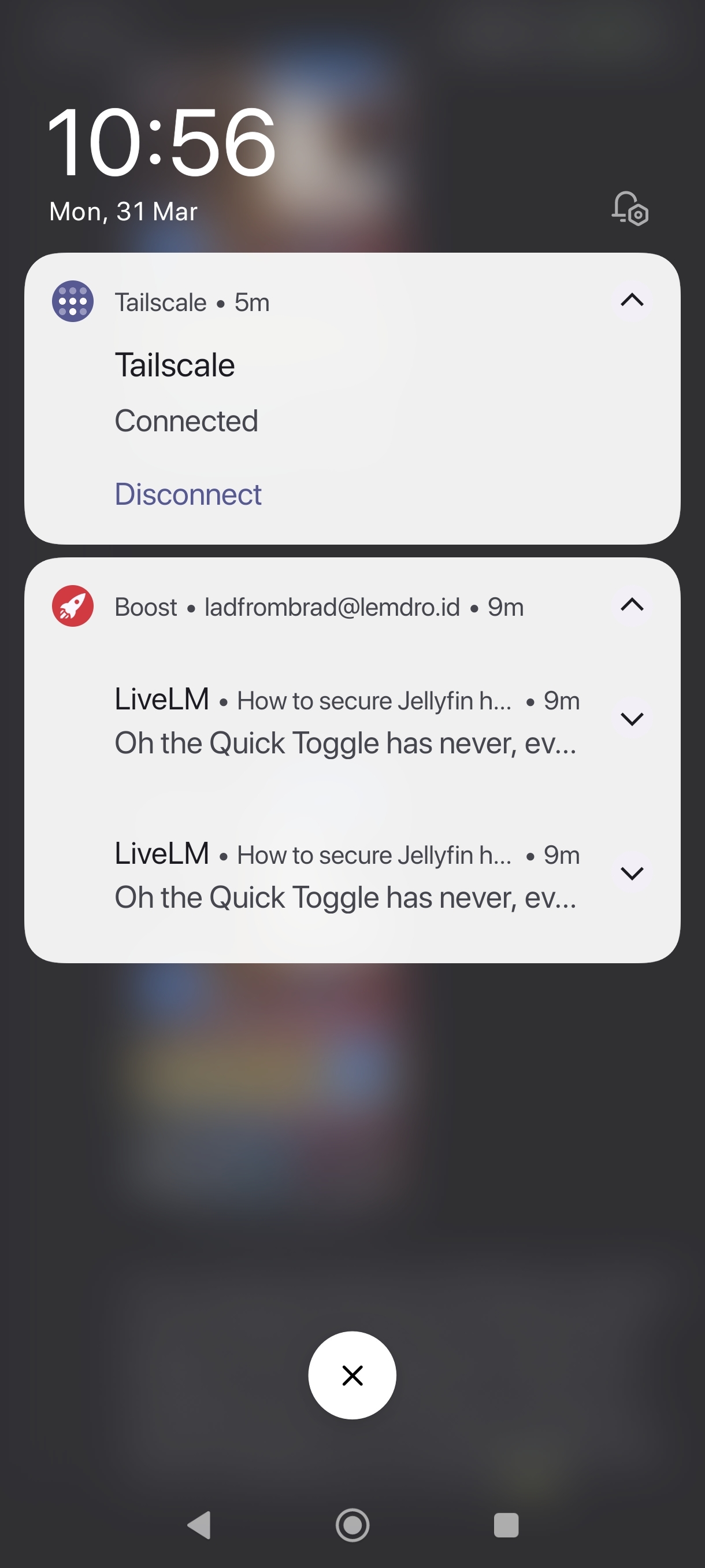
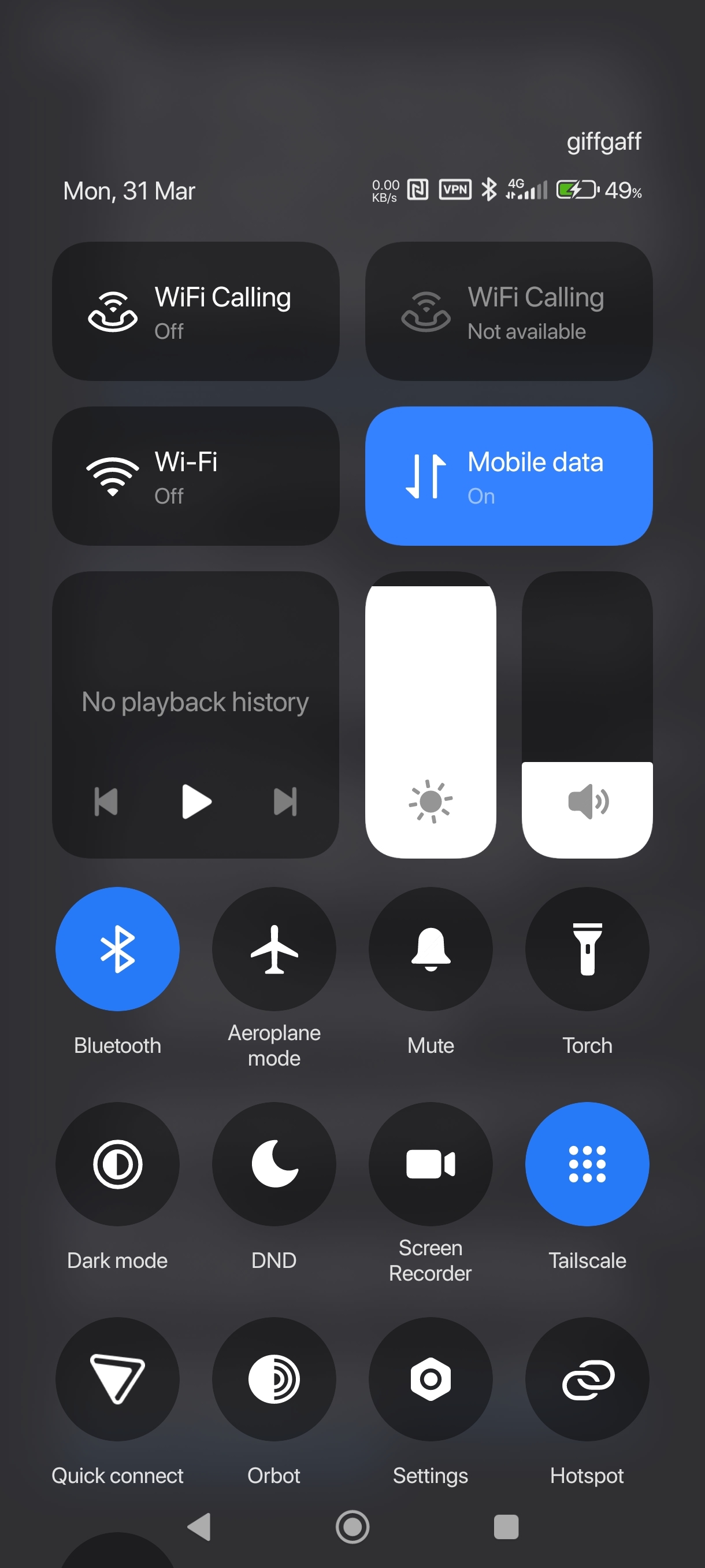 even thou the Quick Toggle and the app itself, shows as running
even thou the Quick Toggle and the app itself, shows as running
If I disconnect/reconnect the notification comes back, and I’ve found something even more weird on my device (A Xiaomi with its infamous OOM / background app killer…) is Tailscale still actually works fine most of the time without the foreground notification. I’m hazarding a 70% of the time for me?
A lot of us a while back found v1.5.2 fugged around with the persistent notification going RIP
Oh the Quick Toggle has never, ever worked correctly. I hoped they fixed it after the UI refresh update but unfortunately not yet.
What device/ROM are you using?
It’s been very iffy for me on and off from Miui > HyperHyperOS, but just checking now?
Works fine
Like I say, the foreground notification seemed to be the lifeline to some of us using it and keeping it alive, even after IIRC some more restrictions came in with future versions of Android (forgive me, I’m very lazy these days and just skim Mishaal’s TG feed 😇)?
e: also
 comment ;)
comment ;)For me it’s always been busted both on AOSP and Miui/HyperOS…
Huh. The nearest I have to an actual “AOSP” device is my King Kong Cubot phone that has probably the cleanest version of “stock Android” I’ve ever seen, and I’m going to presume you mean like a Google Pixel / Graphene etc?
Tailscale and the QS tile / notification was solid on that Cubot but to be honest, I’ve barely turned it on these days and is now one of those drawer phones.
Miui / HyperHyperOS though is a different kettle of fish and exempting Tailscale from its App lel Killer does seem to work. 70-80%ish…
But there is something that just fuggs up and I to like I say turn it off/on like most thingys I own 🙈
I use plain wireguard on me phone, always on essentially with no issues. I wonder why tailscale app can’t stay open.
Same, wireguard with the 'WG Tunnel" app, which adds conditional Auto-Connect. If not on home wifi, connect to the tunnel.
I just stay connected to wireguard even at home, only downside is the odd time I need to chromecast, it needs to be shut off.
I can stay connected, still works, but I don’t think I need the extra hoops.
Oh shit, you may have just solved my only issue with Symfonium
Can you add a split tunnel for just the Chromecast app (I presume that’s how it works idk I don’t use Chromecast) so that just that specific app always ignores your VPN?
conditional Auto-Connect. If not on home wifi, connect to the tunnel.
You don’t need this with Tailscale since it uses a separate IP range for the tunnel.
I also have a different subnet for WG. Not sure I understand what you’re saying…
If you have a separate subnet for it, then why do you only want it to be connected when you’re not on home wifi? You can just leave it connected all the time since it won’t interfere with accessing anything outside that subnet.
One of the main benefits of Wireguard (and Tailscale) is that it’s peer-to-peer rather than client-server. You can use the VPN IPs at home too, and it’ll add barely any overhead.
(leaving it connected is assuming you’re not routing all your traffic through one of the peers)
My network is not publicly accessible. I can only access the internal services while connected to my VPN or when I’m physically at home. I connect to WG to use the local DNS (pihole) or to access the selfhosted stuff. I don’t need to be connected while I’m at home… In a way, I am always using the home DNS.
Maybe I’m misunderstanding what you’re saying…
I suspect that it goes down and stays down whenever there is an app update, but I haven’t confirmed it yet.
Does the plain wireguard app stay up during updates?
Android wireguard all hasn’t been updated in 18mo. Its extremely simple with a small code base. There basically isn’t anything to update. It uses wireguard kernel module which is itself is only like 700 lines of code. It so simple that it basically became stable very quickly and there is nothing left of update right now.
https://git.zx2c4.com/wireguard-android/about/
I personally get the from obtainium to bypass play store
If you make Tailscale your VPN in Android it will never be killed. Mileage may vary depending on flavor of Android. I’ve used this on stock Pixel and GrapheneOS.
Under Settings > Network and internet > VPN
Tap the Cog icon next to Tailscale and select Always-on VPN.
Holy moly, I did not know this existed! Thanks! Just turned this on!
Look up your phone on dontkillmyapp.com and make sure tailscale is excluded from battery and network “optimization”.
Have you tried disabling battery optimization for tailscale?
I did this and it still seems to randomly disconnect.
Maybe headscale will do better?
Headscale is a replacement for the coordination servers, which are only used to distribute configs and help nodes find each other. It won’t change client-side behaviour.
I use fail2ban to ban IPs that fall to login and also IPs that perform common scans in the reverse proxy
also have jellyfin disable the account after a number of failed logins.
You could put authentik in front of it too
I think that breaks most clients
Yes, it breaks native login, but you can authenticate with Authentik on your phone for example, and use Quick connect to authorize non-browser sessions with it.
? How does putting something before it break it? It most certainly doesn’t.
Clients are built to speak directly to the Jellyfin API. if you put an auth service in front it won’t even ask you to try and authenticate with that.
Wireguard (or tailscale) would be best here.
OpenVPN
Or wireguard, depending where & how they want to implement it might be simpler or better/worse on hardware.
setup a WAF appliance and forward traffic through it to your current installation.
WAF??
web application firewall.
think of it like an intelligent firewall proxy that can take action against perceived threats like injection attacks or timed attacks. some can also help fight against DDOS when integrated with an actual firewall upstream.
CloudFlare tunnel with Zero Trust, plus their bot and abuse blocking. Users can get in with the right oauth, plus only allowed from the countries I know they’re in. Then just their username and password on jellyfin.
Using cloudflare tunnels means nothing is encrypted and cloudflare sees all.
Oh no they’ll see I’m watching TNG
Doesn’t streaming media over a cloudflare tunnel/proxy violate their ToS
🤫
No, they removed that clause some 2 or 3 years back.
They prohibit large amounts of media being streamed, and they reserve the right to suspend or terminate accounts for it. Multiple years in, that has not happened.
Edit: here, you can read https://blog.cloudflare.com/updated-tos/
Cloudflare is known for being unreliable with how and when it enforces the ToS (especially for paying customers!). Just because they haven’t cracked down on everyone doesn’t mean they won’t arbitrarily pick out your account from thousands of others just to slap a ban on. There’s inherent risk to it
I hate the cloudflare stuff making me do captchas or outright denying me with a burning passion. My fault for committing the heinous crime of using a VPN!
Skill issue
just run wireguard on the jelly server…
My users aren’t going to figure that out.
they don’t have to figure it out, you are the one running it
They’d have to connect to it, and possibly reconnect. That aspect is the issue.
I use Pangolin (https://github.com/fosrl/pangolin)
I was thinking of setting this up recntly after seeing it on Jim’s garage. Do you use it for all your external services or just jellyfin? How does it compare to a fairly robust WAF like bunkerweb?
URL is 404
remove the brace at the end
My setup: Locally (all in docker):
- JF for managing and local access
- JF with read only mounted volumes that uses the network of my Wireguard client container
- Wireguard client opening a tunnel to Wireguard server on VPS ** Ping container regularly doing pings to Wireguard Server so the connection stays up (didn’t manage it otherwise)
VPS (Oracle Cloud free tier, also everything in docker):
- Caddy as a reverse proxy with https enabled and geolocking (only certain countries are allowed to connect to)
- fail2ban to block IPs that try to bruteforce credentials
- Wireguard server
Usernames are not shown in the frontend and have to be entered. Passwords are generated by a password manager and can’t be changed by the user.
So my clients just get the URL of my reverse proxy and can access the read only JF through my Wireguard tunnel. Didn’t have to open any ports on my side. If someone is interested I can share the docker compose files later.
This seems like a developer/infrastructure level job, any dumb down step by step procedure to recommend?
https://codeberg.org/skjalli/jellyfin-vps-setup here you go, took me longer than expected and I hope it’s helpful, might contain a few errors since I had to remove some settings but I guess this should work.
Thank you! Impressive documentation work, looks like I have to learn docker first.
It’s a steep learning curve for sure but once you get the basics it’s straight forward until you hit very specific problems.
Are you a Windows or Linux user? They often want to push their Docker UI application but in my opinion docker engine with docker compose is enough. There are probably a lot of great tutorials out there and I can recommend https://www.linuxserver.io/ for images.
I am currently in the ptocess to document my docker fioes and upload them to codeberg with a readme, it takes a bit, will let you know once I am done
I’m more interested in the fail2ban setup. How did you do that for Jellyfin? Is it through a plugin?
It’s a separate container, currently in the process of writing everything up, will update once done
Thanks!
https://codeberg.org/skjalli/jellyfin-vps-setup here you go, took me longer than expected and I hope it’s helpful, might contain a few errors since I had to remove some settings but I guess this should work.
Thanks! I’ll read more through it when I have the chance!
I am interested in your docker compose
https://codeberg.org/skjalli/jellyfin-vps-setup here you go, took me longer than expected and I hope it’s helpful, might contain a few errors since I had to remove some settings but I guess this should work.
This is honestly awesome! I was thinking about a similar setup for a long time but wasn’t sure how to do this exactly, this seems exactly like the setup I was looking for. Thank you!
You’re welcome, happy that I can help. I also just updated it a bit. In case you find any issues or have questions please let me know. It was mostly trial and error until it ran…
Will share this evening after work.
Whats your setup? I just Ngnix Proxy Manager, Jellyfin etc in Docker. Modify ufw rules and also install this on the server (linux) https://github.com/friendly-bits/geoip-shell
Jellyfin is secure by default, as long as you have https. Just chose a secure password
No, it isn’t.
I wouldn’t say “great” it’s ok software. Not even due to all of those security things which is a nightmare too. They do things like break the search speed months ago and not have any idea why, it’s so insanely slow and on top of that it somehow lags the entire client when searching too, not just the server which is the only thing doing the query. Lots of issues just with that.
Oh boy. Nope. My friends gonna have to fiddle with a VPN, forget exposing JF to the outside…
Some of these are bonkers. The argument not to fix them because of backwards compatibility is even wilder. Which normal client would need the ability to get data for any other account that it hasn’t the Auth token for.
Just make a different API prefix that’s secure and subject to change, and once the official clients are updated, deprecate the insecure API (off by default).
That way you preserve backwards compatibility without forcing everyone to be insecure.
Even just basic API versioning would be sufficient. .NET offers a bunch of ways to handle breaking changes in APIs
Wtf. Thank you
I’ve put it behind WireGuard since only my wife and I use it. Otherwise I’d just use Caddy or other such reverse proxy that does https and then keep Jellyfin and Caddy up to date.
What I used to do was: I put jellyfin behind an nginx reverse proxy, on a separate vhost (so on a unique domain). Then I added basic authentication (a htpasswd file) with an unguessable password on the whole domain. Then I added geoip firewall rules so that port 443 was only reachable from the country I was in. I live in small country, so this significantly limits exposure.
Downside of this approach: basic auth is annoying. The jellyfin client doesn’t like it … so I had to use a browser to stream.
Nowadays, I put all my services behind a wireguard VPN and I expose nothing else. Only issue I’ve had is when I was on vacation in a bnb and they used the same IP range as my home network :-|













